
What to know:
- ZetaChain exploit exposed a flaw in cross-chain messaging.
- Attack drained only internal team wallets, not user funds.
- Developers patched the vulnerability before wider damage.

ZetaChain current situation presents two different numerical results. Cross-chain systems allow users to transfer value between different systems but their design expands the potential security threats which attackers can exploit. The lesson came the hard way.
An attacker used a major security flaw in its smart contract system to gain control over its cross-chain communication network. The result was swift. Internal team wallets suffered complete fund loss. The larger ecosystem maintained its complete functioning. Developers moved fast. They closed the security hole before any user funds got compromised.
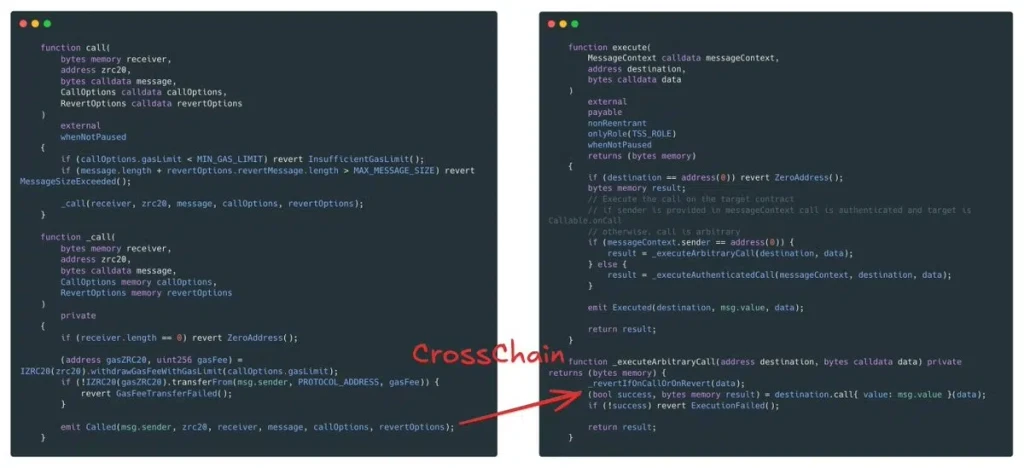
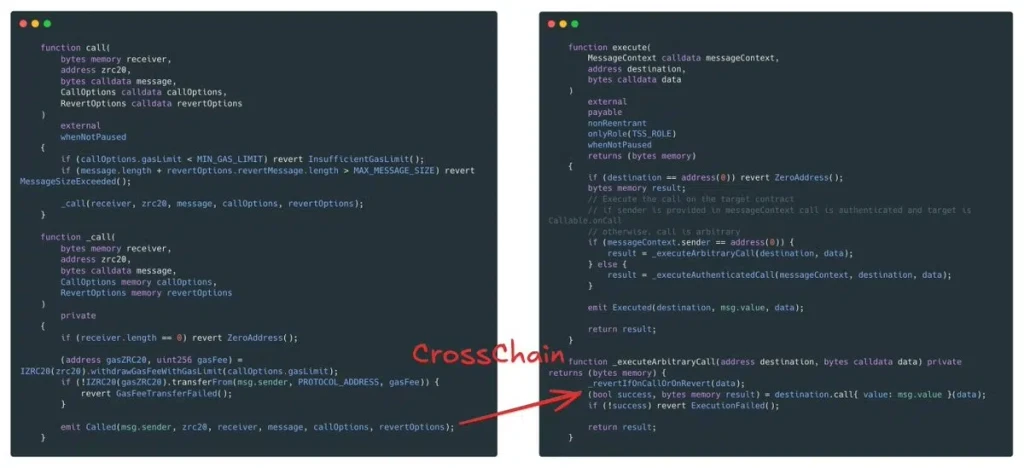
Security firm SlowMist identified the main problem. The defect occurred within the GatewayZEVM contract. The problem existed within its call function. The system did not implement any protective mechanisms. The system had no methods to control who could access it.
The system did not have any procedures to guarantee proper handling of incoming data. The missing component in the trustless execution framework created an expensive security issue.
Also Read: 2024 Crypto Insights: Chainlink, ZetaChain, and GameStop Memes are the Best Bets
ZetaChain Vulnerability Exposed
The weakness was simple but dangerous. Any user could bypass restrictions. The users had the ability to make unauthorized cross-chain calls. That opened the door to abuse.
The attacker created a harmful transaction. It was not random. It was precise. The call was designed to emit a fake cross-chain event. The event created the appearance of genuine network operations.
ZetaChain’s relayer responded to the deception. Its design enables it to monitor. The system requires it to perform. The system must carry out cross-chain commands. The system achieved its intended purpose. The system detected the fraudulent signal and executed it on the target blockchain. The process resulted in a successful theft of money.
ZetaChain Response Limits Damage
The response was fast and clear. ZetaChain developers blocked the attack vector. They confirmed the damage was contained. The only impact affected internal wallets. User funds remained safe.
The distinction holds importance. Trust in crypto systems shows extreme vulnerability. User asset breaches will lead to market panic. Here, that line held.
The lesson remains extremely clear. Interoperability shows its strength. The system requires total security for its operation. The system needs to protect all its functions. The system needs to evaluate all its inputs.
ZetaChain needs to overcome its current challenge. The challenge requires both technological and trust evaluation. The market will judge how it regains trust because this value matters more than the original exploitation.
Also Read: Token Unlock of $5M+ for SUI, OMNI in Next Week: Volatility Ahead




Be the first to comment